Book contents
- Frontmatter
- Contents
- Preface
- Acknowledgments
- 1 Introduction
- 2 Modular Arithmetic
- 3 The Addition Cypher, an Insecure Block Cypher
- 4 Functions
- 5 Probability Theory
- 6 Perfect Secrecy and Perfectly Secure Cryptosystems
- 7 Number Theory
- 8 Euclid's Algorithm
- 9 Some Uses of Perfect Secrecy
- 10 Computational Problems, Easy and Hard
- 11 Modular Exponentiation, Modular Logarithm, and One-Way Functions
- 12 Diffie and Hellman's Exponential-Key-Agreement Protocol
- 13 Computationally Secure Single-Key Cryptosystems
- 14 Public-Key Cryptosystems and Digital Signatures
- Further Reading
- Index
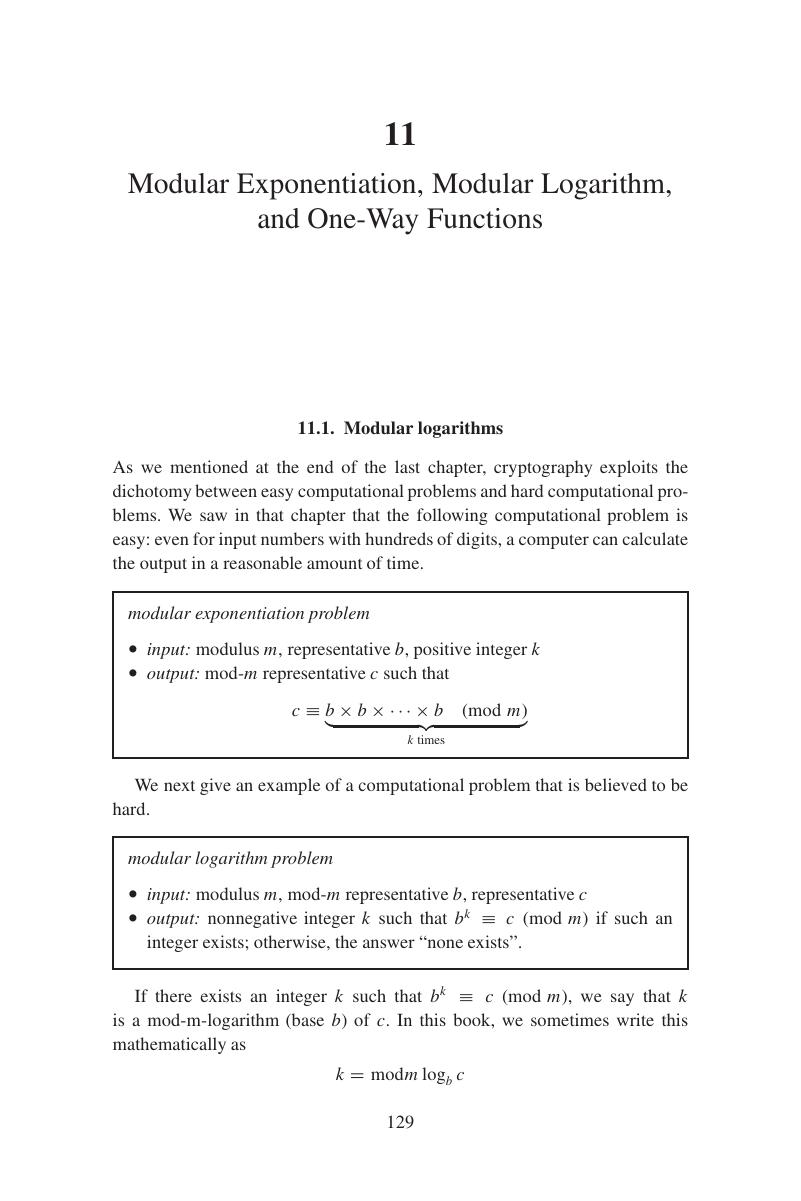
11 - Modular Exponentiation, Modular Logarithm, and One-Way Functions
Published online by Cambridge University Press: 05 July 2014
- Frontmatter
- Contents
- Preface
- Acknowledgments
- 1 Introduction
- 2 Modular Arithmetic
- 3 The Addition Cypher, an Insecure Block Cypher
- 4 Functions
- 5 Probability Theory
- 6 Perfect Secrecy and Perfectly Secure Cryptosystems
- 7 Number Theory
- 8 Euclid's Algorithm
- 9 Some Uses of Perfect Secrecy
- 10 Computational Problems, Easy and Hard
- 11 Modular Exponentiation, Modular Logarithm, and One-Way Functions
- 12 Diffie and Hellman's Exponential-Key-Agreement Protocol
- 13 Computationally Secure Single-Key Cryptosystems
- 14 Public-Key Cryptosystems and Digital Signatures
- Further Reading
- Index
Summary
- Type
- Chapter
- Information
- A Cryptography PrimerSecrets and Promises, pp. 129 - 142Publisher: Cambridge University PressPrint publication year: 2014