Book contents
- Frontmatter
- Contents
- Preface
- 1 Introduction
- 2 From Julius Caesar to simple substitution
- 3 Polyalphabetic systems
- 4 Jigsaw ciphers
- 5 Two-letter ciphers
- 6 Codes
- 7 Ciphers for spies
- 8 Producing random numbers and letters
- 9 The Enigma cipher machine
- 10 The Hagelin cipher machine
- 11 Beyond the Enigma
- 12 Public key cryptography
- 13 Encipherment and the internet
- Appendix
- Solutions to problems
- References
- Name index
- Subject index
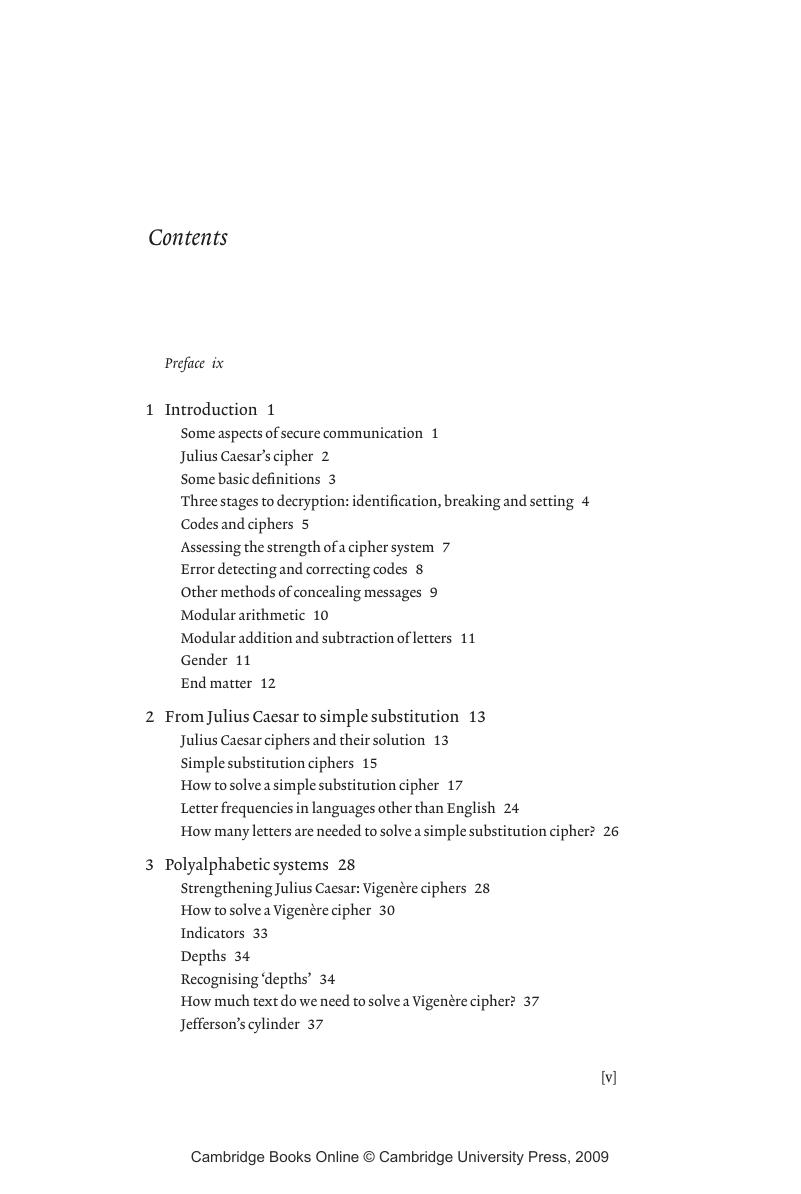
Contents
Published online by Cambridge University Press: 13 August 2009
- Frontmatter
- Contents
- Preface
- 1 Introduction
- 2 From Julius Caesar to simple substitution
- 3 Polyalphabetic systems
- 4 Jigsaw ciphers
- 5 Two-letter ciphers
- 6 Codes
- 7 Ciphers for spies
- 8 Producing random numbers and letters
- 9 The Enigma cipher machine
- 10 The Hagelin cipher machine
- 11 Beyond the Enigma
- 12 Public key cryptography
- 13 Encipherment and the internet
- Appendix
- Solutions to problems
- References
- Name index
- Subject index
Summary
- Type
- Chapter
- Information
- Codes and CiphersJulius Caesar, the Enigma, and the Internet, pp. v - viiiPublisher: Cambridge University PressPrint publication year: 2001