Book contents
- Frontmatter
- Contents
- Foreword
- Preface
- Acknowledgments
- 1 Introduction
- 2 Classical cryptography
- 3 Information theory
- 4 Quantum information theory
- 5 Cryptosystems based on quantum key distribution
- 6 General results on secret-key distillation
- 7 Privacy amplification using hash functions
- 8 Reconciliation
- 9 Non-binary reconciliation
- 10 The BB84 protocol
- 11 Protocols with continuous variables
- 12 Security analysis of quantum key distribution
- Appendix symbols and abbreviations
- Bibliography
- Index
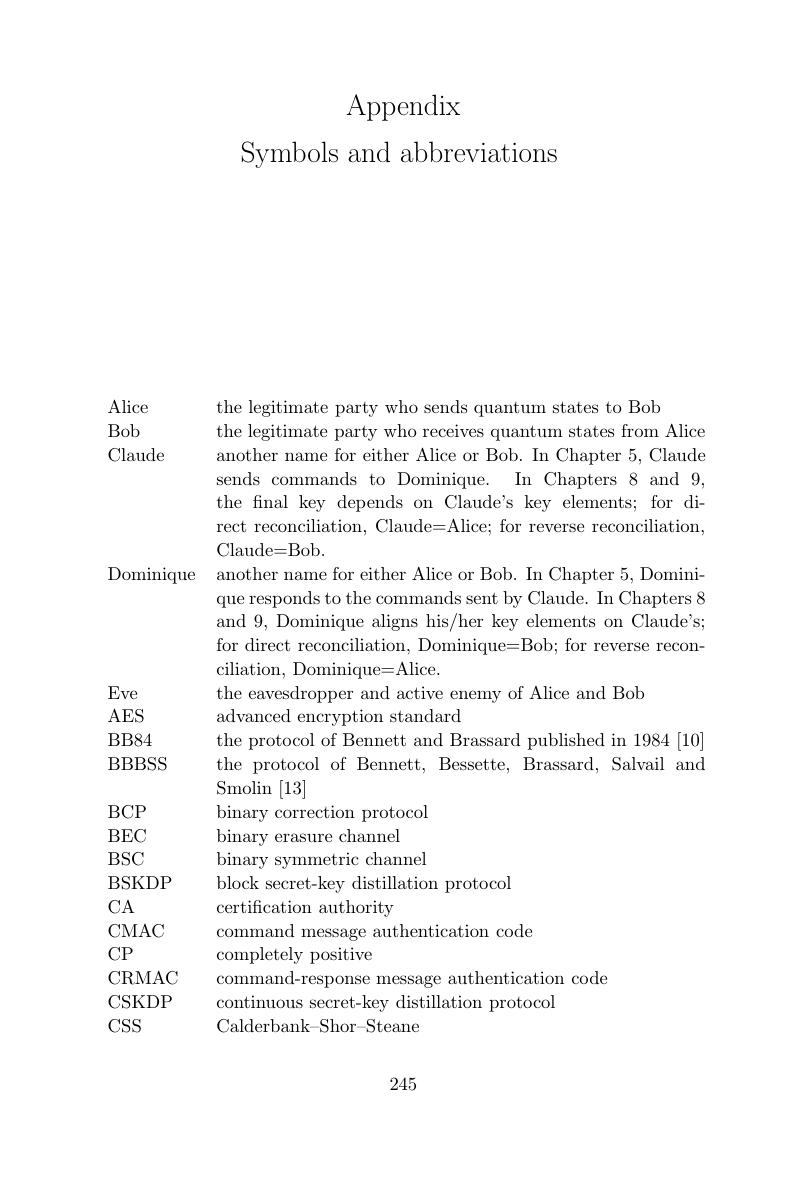
Appendix - symbols and abbreviations
Published online by Cambridge University Press: 04 August 2010
- Frontmatter
- Contents
- Foreword
- Preface
- Acknowledgments
- 1 Introduction
- 2 Classical cryptography
- 3 Information theory
- 4 Quantum information theory
- 5 Cryptosystems based on quantum key distribution
- 6 General results on secret-key distillation
- 7 Privacy amplification using hash functions
- 8 Reconciliation
- 9 Non-binary reconciliation
- 10 The BB84 protocol
- 11 Protocols with continuous variables
- 12 Security analysis of quantum key distribution
- Appendix symbols and abbreviations
- Bibliography
- Index
Summary
- Type
- Chapter
- Information
- Quantum Cryptography and Secret-Key Distillation , pp. 245 - 248Publisher: Cambridge University PressPrint publication year: 2006